
Towing the line between keeping your private information secure and still conveniently accessible is always a challenge, but you can make it a little easier—and fun—by coming up with your own simple encryption schemes that you can decode easily in your head. Here's a look at how it's done and why you'd want to do it.
What Is Encryption?
Encryption is the process of encoding a message, and that process can take many forms.
Microsoft offers a good definition:
Encryption is the name given to the process of applying an algorithm to a message, which scrambles the data in it-making it very difficult and time consuming, if not practically impossible, to deduce the original given only the encoded data. Inputs to the algorithm typically involve additional secret data called keys, which prevents the message from being decoded-even if the algorithm is publicly known.
These encryption schemes can be complicated or simple, so long as it's possible to decode them when necessary. In this post we're going to look solely at simple methods that are easy to remember, easy to decode, and near impossible to crack.
Why Bother with Encryption?

Every now and then you need your social security, credit card, or account number that you don't want the world to know. That said, that information has to exist
somewhere otherwise you're never going to be able to use it. You can memorize numbers, but you can't count on your memory as the only source as
we can't even remember what we see with much accuracy. Writing down those numbers makes them available for all to see and locking them away is inconvenient. Encrypting them, however, is a good compromise. That way you can carry around important information with you at all times or even leave it out in the open without worrying about anyone stealing it.
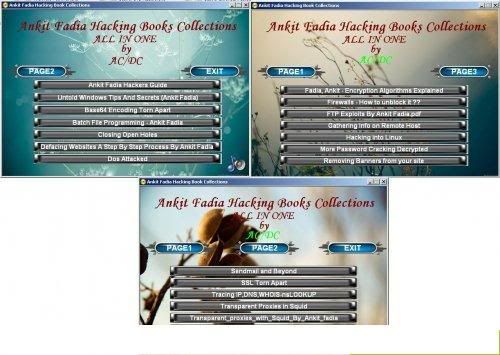
Existing Encryption Schemes That Are Effective

One of my favorite simple schemes for encrypting numbers comes from (amateur) mathematician
Pierre de Fermat. He once posed an interesting puzzle, asking the order of numbers. Here's an example:
8 5 4 9 1 7 6 3 2 The order of those numbers is alphabetical, meaning the first letter (or two) of each number corresponds to its place in the string above. 8 is "E", 5 is "F", 4 is also "F", 9 is "N", and so on. It all comes out to:
E Fi Fo N O Se Si Th Tw This points to a pretty decent encryption scheme. If you wrote out an account number as EFiFoNOSeSiThTw and someone were to see it, chances are they'd have no idea what it meant. On the other hand, you'd be able to decode the message in a few seconds for any time you needed that account number.
The same kind of scheme works well for alphanumeric encryption. If the information you want to protect was
HAPPY 30TH BIRTHDAY, you could simply switch the letters for numbers and the numbers for letters like this:
81161625 ThZ208 29182084125 Like with the previous example, numbers were replaced with the first letter they're spelled with (or two if necessary). Letters were replaced with the numeric order in the alphabet (H=8, A=1, P=16, P=16, Y=25, etc.).
These are both very simple encryption schemes that pretty much everyone would see as gibberish but you'd be able to decode fairly quickly when needed. You could even use a scheme like this to create secure passwords. We've learned that multi-word phrases already make more secure passwords, and you could easily use this kind of encryption scheme to encode the name of a web site plus a common number of your choice, such as
1296581311518 TwZZFi . This would make for unique, secure passwords that you could easily store in a service like
LastPass, forget, and easily figure out in the event of a data failure. That's just one example of how your own alphanumeric encryption scheme can be useful.
Creating Your Own Encryption Schemes
Of course, using these examples is somewhat of a security risk because they're published and anyone reading this post could potentially detect them and decrypt your key. For that reason, it's more secure if you come up with your own idea and keep it secret. When you do, make sure you do the following things:
- Make your encryption scheme something you can easily remember whenever you look at the encoded information. One or two rules/steps should be enough. If you make too many rules/steps when creating the scheme it will be much harder to recall when you need to use it to decode your information.
- Show a few samples of encoded information to your smartest friends and see if they're able to decode it within a few minutes.
- Test out your encryption scheme on unimportant information for a few weeks to make sure you remember it after some time has passed. If you don't, you'll need to come up with a more simple scheme that you won't forget.
Once you've got your simple encryption scheme put together you can start writing your codes in publicly-visible places without the need to worry about thieves or privacy concerns.
U Can Download Any Videos, All cracked Applications, Games in the net & also with Various Features.
Click Here to Try ScienceHack ToolBar...



































 Towing the line between keeping your private information secure and still conveniently accessible is always a challenge, but you can make it a little easier—and fun—by coming up with your own simple encryption schemes that you can decode easily in your head. Here's a look at how it's done and why you'd want to do it.
Towing the line between keeping your private information secure and still conveniently accessible is always a challenge, but you can make it a little easier—and fun—by coming up with your own simple encryption schemes that you can decode easily in your head. Here's a look at how it's done and why you'd want to do it.  Every now and then you need your social security, credit card, or account number that you don't want the world to know. That said, that information has to exist somewhere otherwise you're never going to be able to use it. You can memorize numbers, but you can't count on your memory as the only source as
Every now and then you need your social security, credit card, or account number that you don't want the world to know. That said, that information has to exist somewhere otherwise you're never going to be able to use it. You can memorize numbers, but you can't count on your memory as the only source as  One of my favorite simple schemes for encrypting numbers comes from (amateur) mathematician
One of my favorite simple schemes for encrypting numbers comes from (amateur) mathematician 

